Review of Existing Analysis Tools for SELinux Security Policies: Challenges and a Proposed Solution | SpringerLink
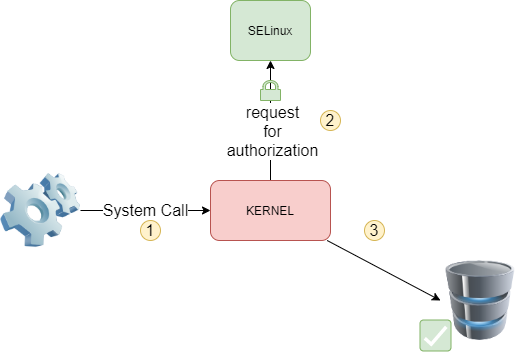
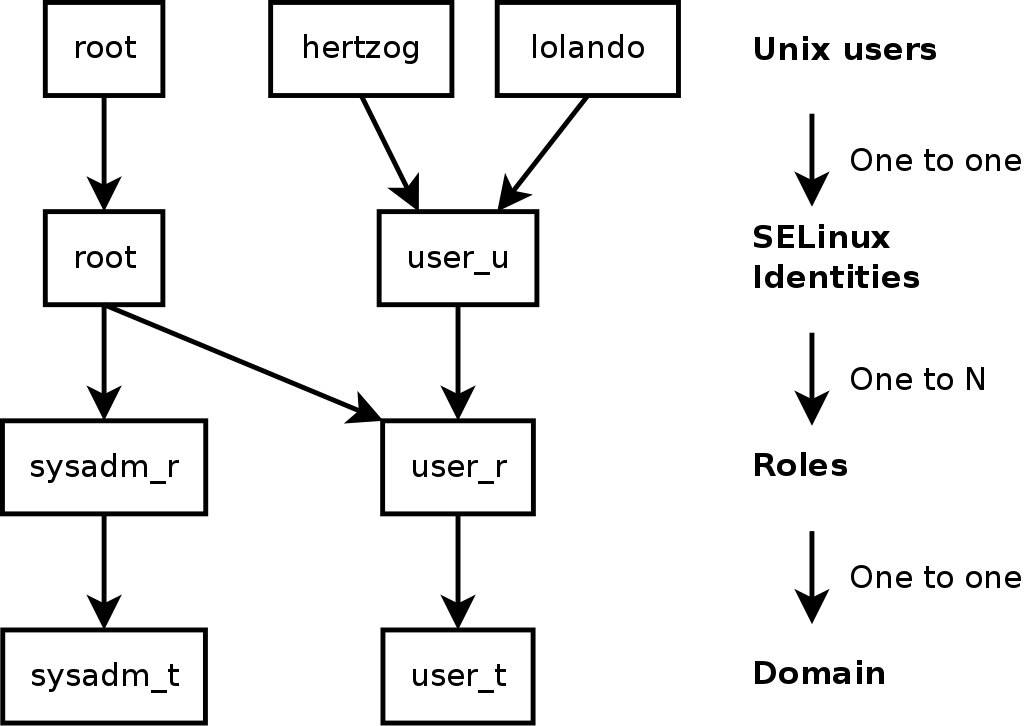
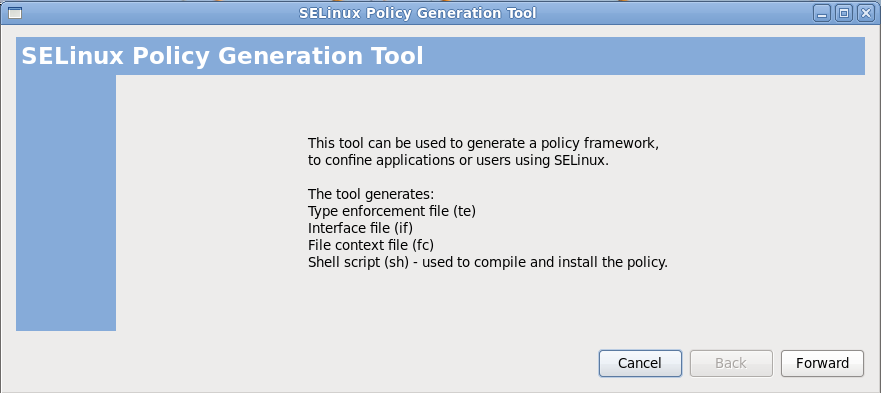
Exploring SELinux: Enhancing Security Through Mandatory Access Control | by Suraj Singh Bisht | Stackademic
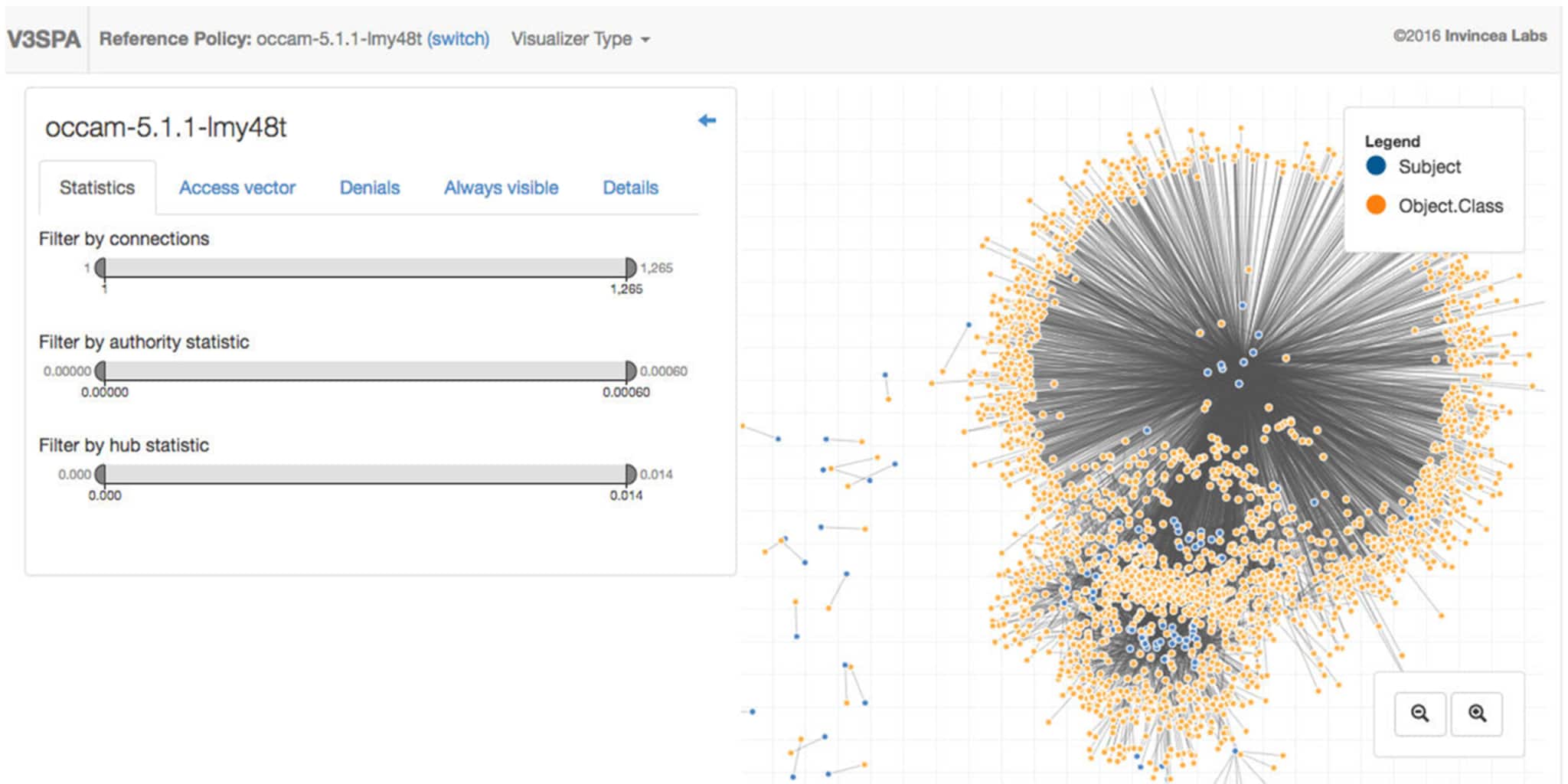
V3SPA: An Open Source Tool for Visually Analyzing and Diffing SELinux/SE for Android Security Policies - Two Six Technologies








![Illustration] Introduction to SELinux – How it works? Explanation of the Basic knowledge – | SEの道標 Illustration] Introduction to SELinux – How it works? Explanation of the Basic knowledge – | SEの道標](https://milestone-of-se.nesuke.com/wp-content/uploads/2018/07/en-selinux-summary-1.png)