Obfuscation Techniques Ppt Powerpoint Presentation Styles Ideas Cpb | Presentation Graphics | Presentation PowerPoint Example | Slide Templates

Practical Reverse Engineering: x86, x64, ARM, Windows Kernel, Reversing Tools, and Obfuscation : Dang, Bruce: Amazon.fr: Livres
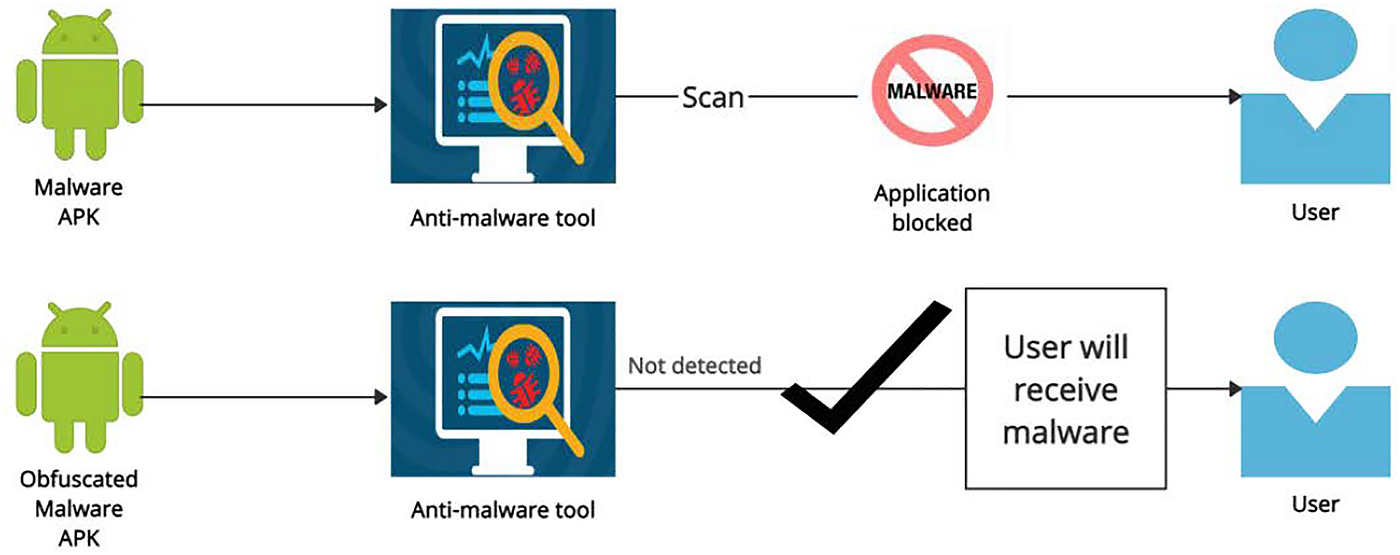
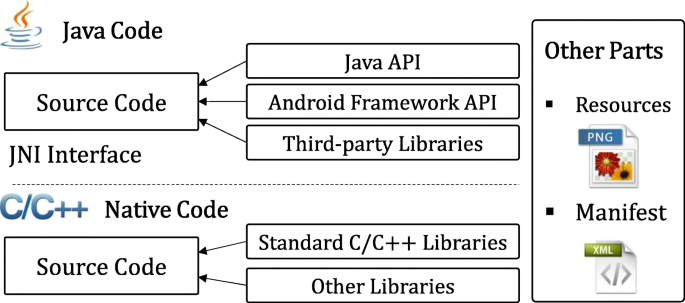
GitHub - Dgeeth9595/Android-Obfuscation-Tools: Android Obfuscation tools that work at dalvik bytecode level.
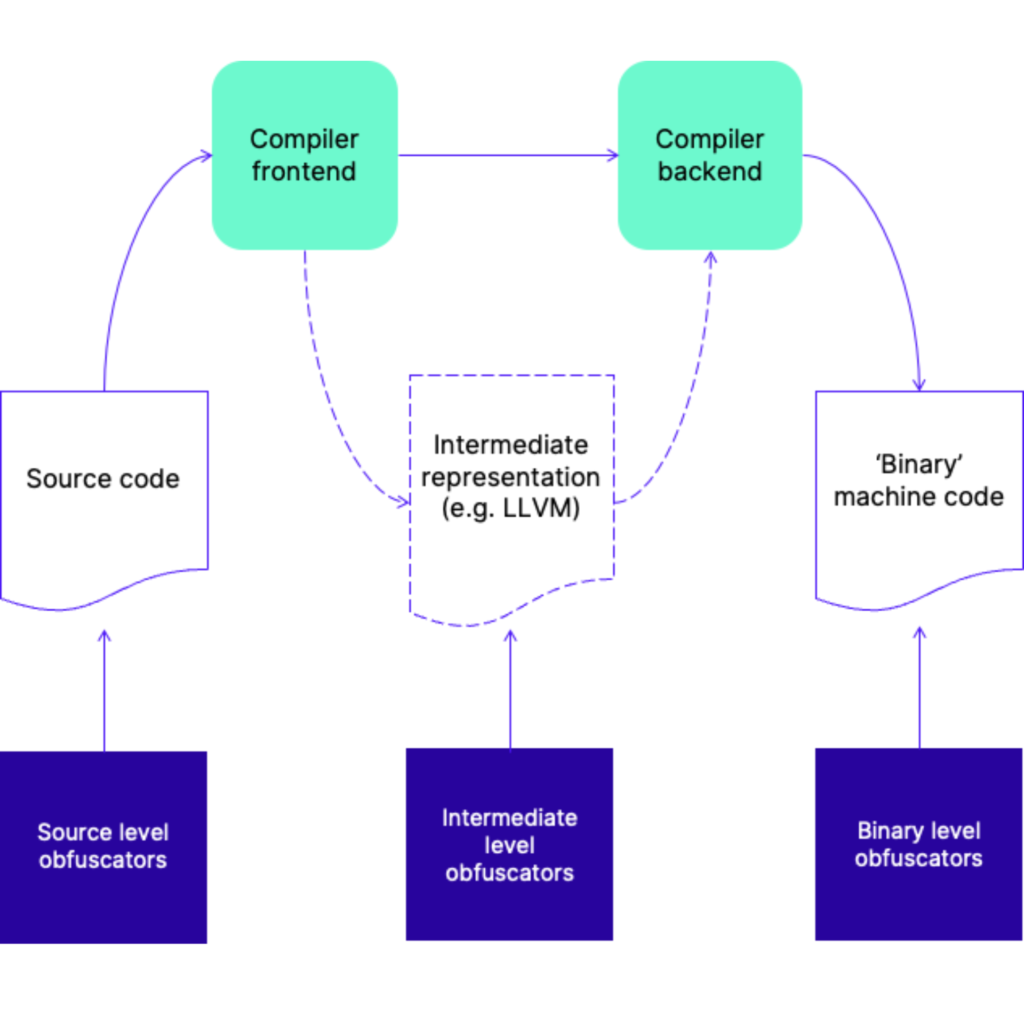
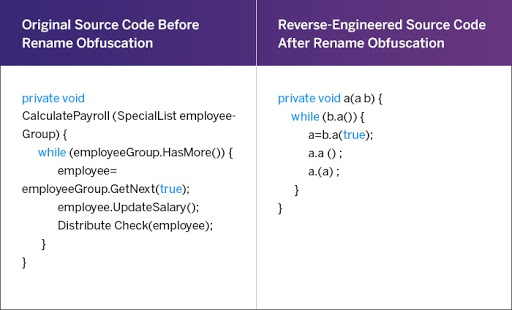
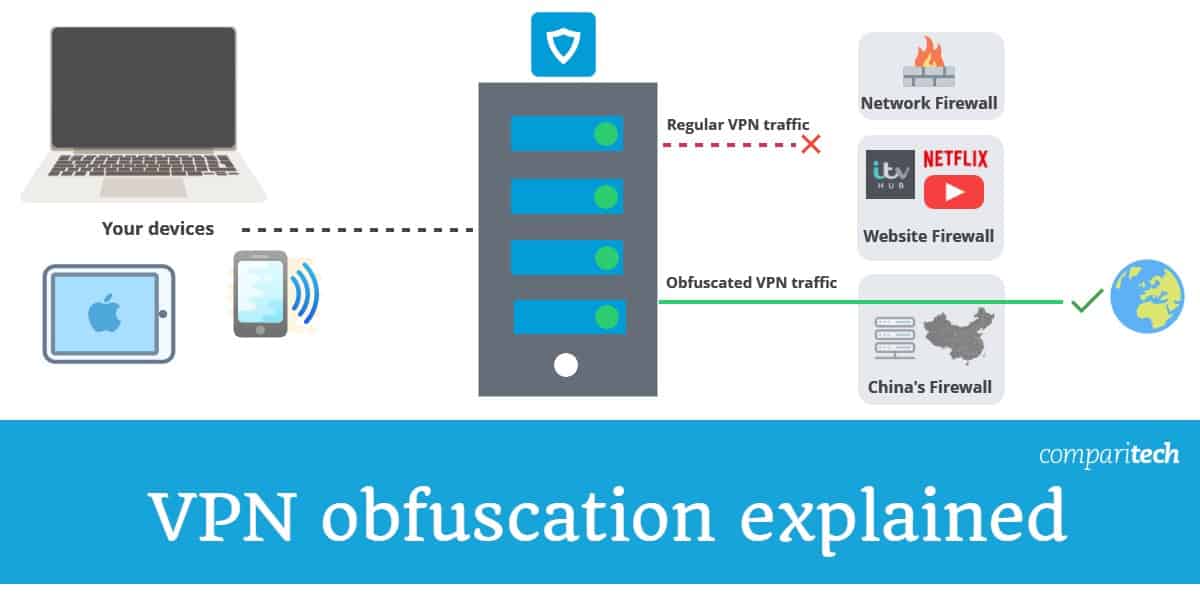
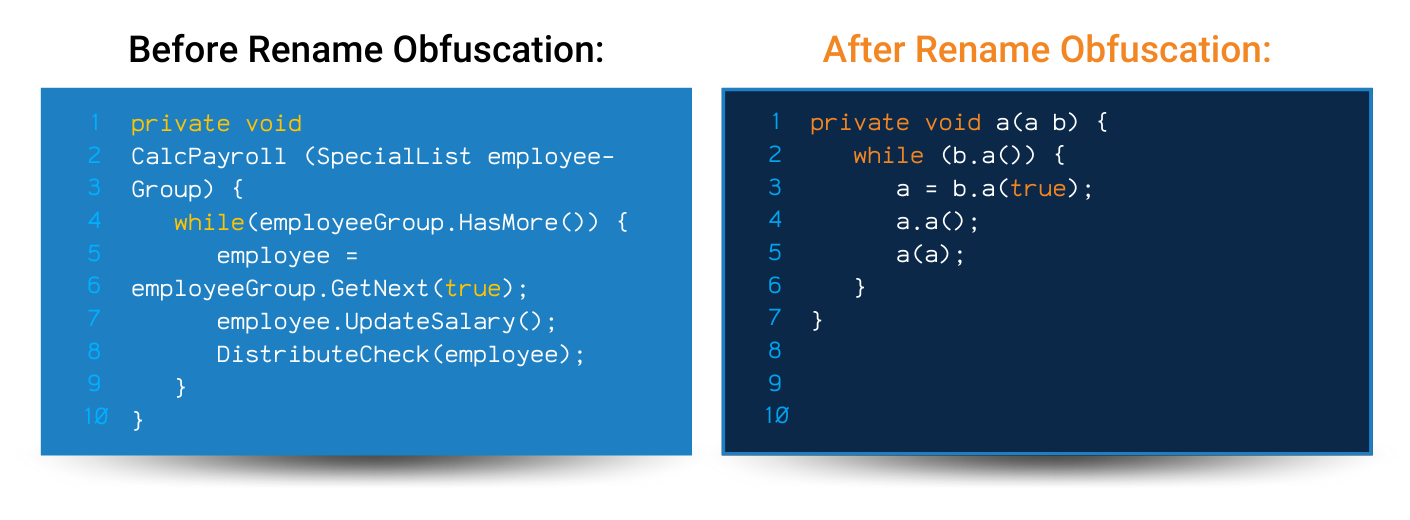
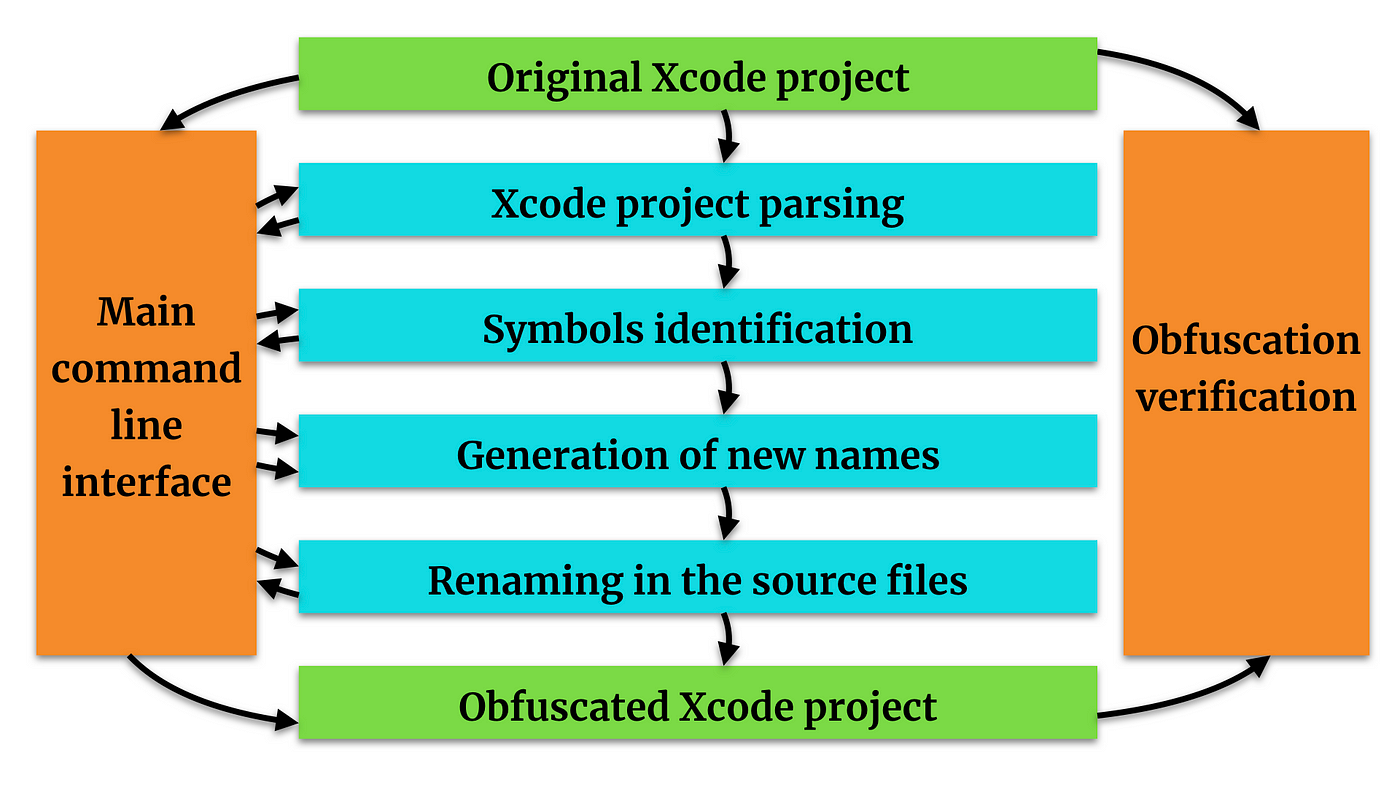
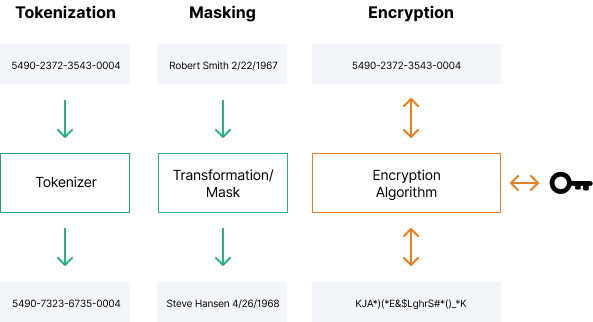
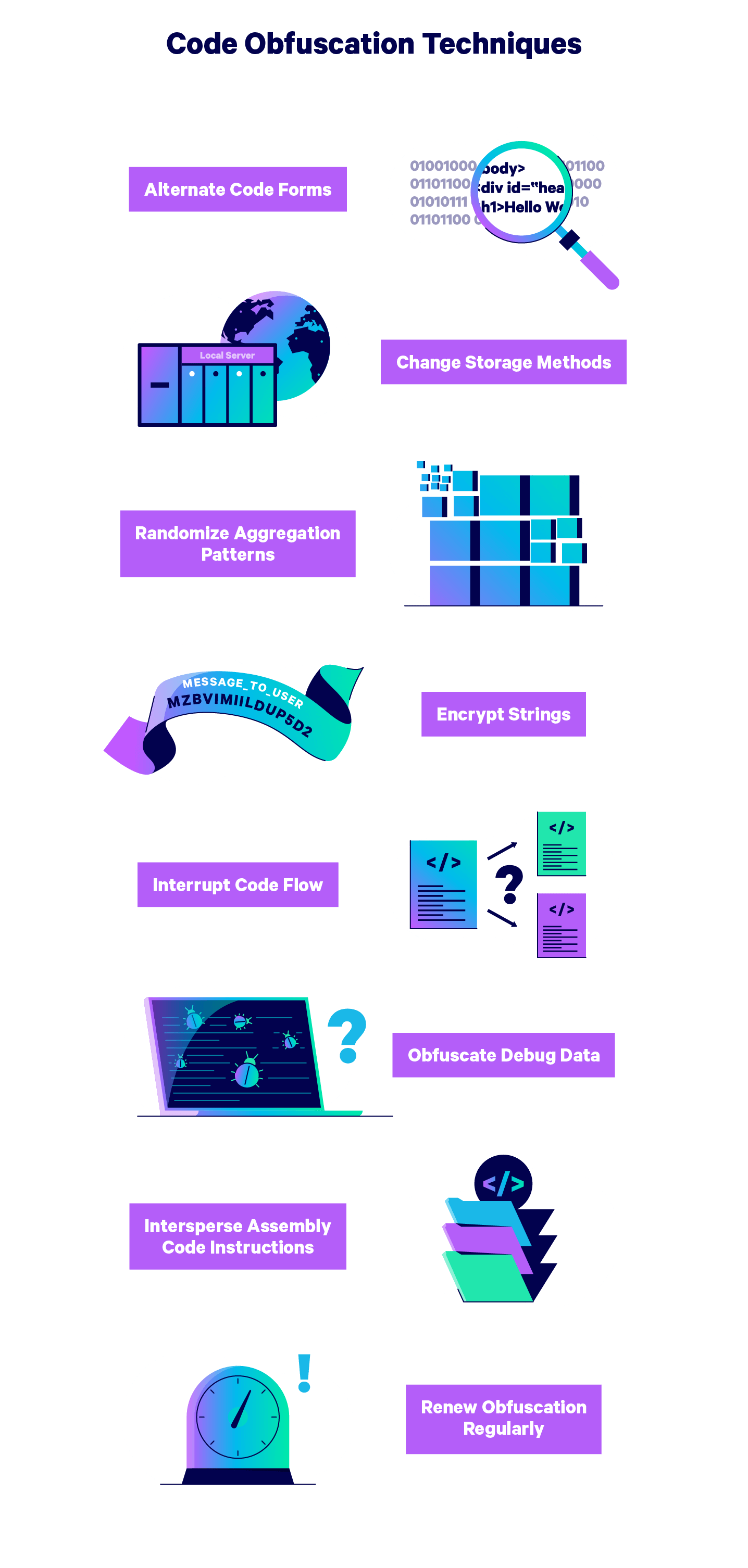
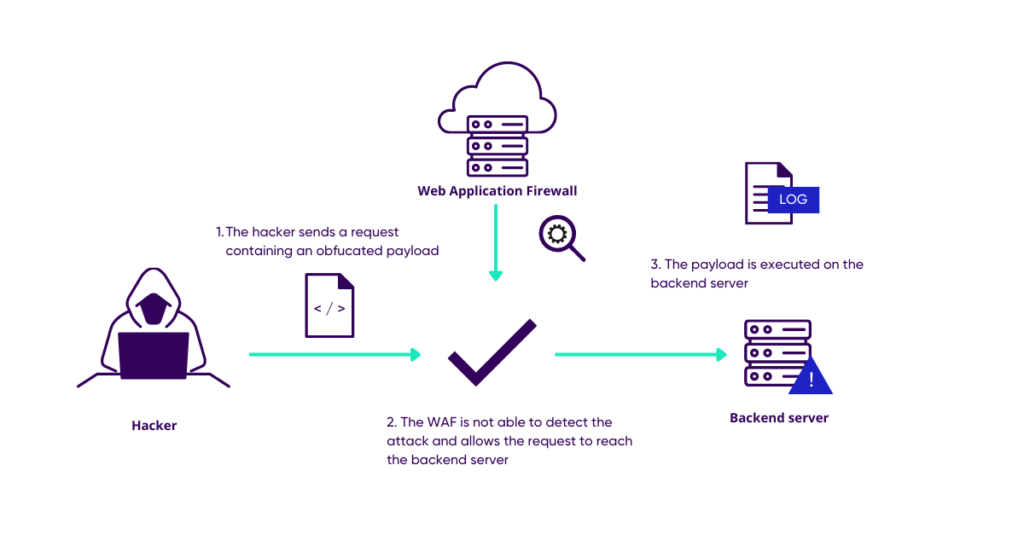
Layered obfuscation: a taxonomy of software obfuscation techniques for layered security | Cybersecurity | Full Text