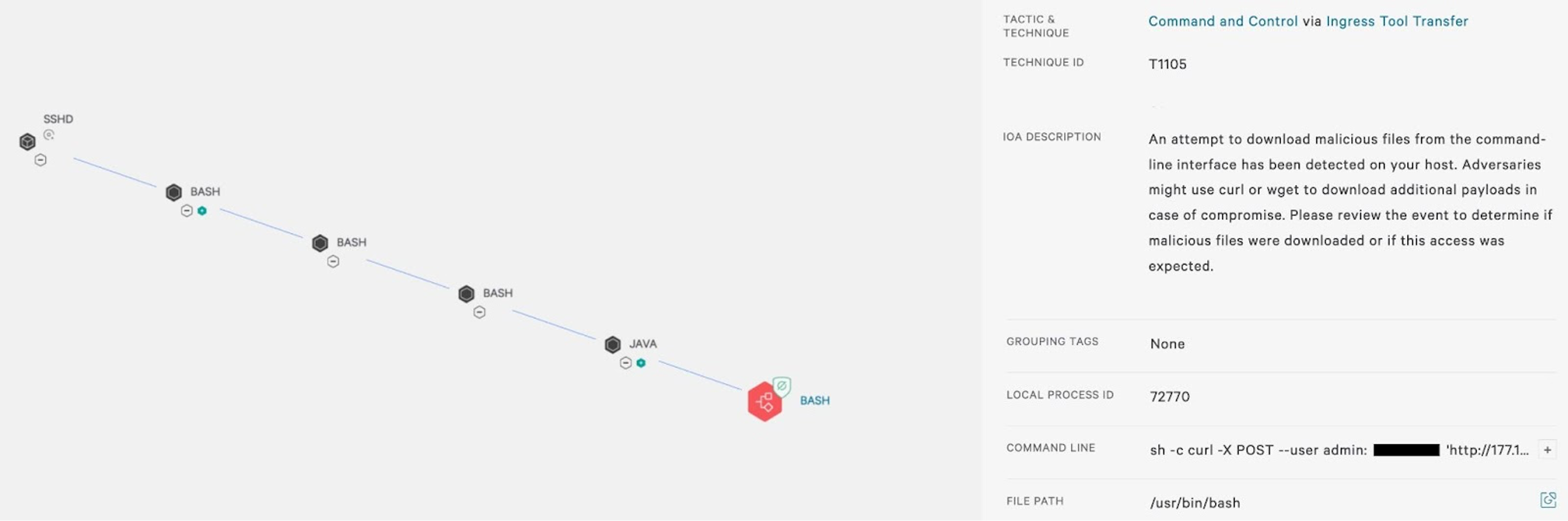
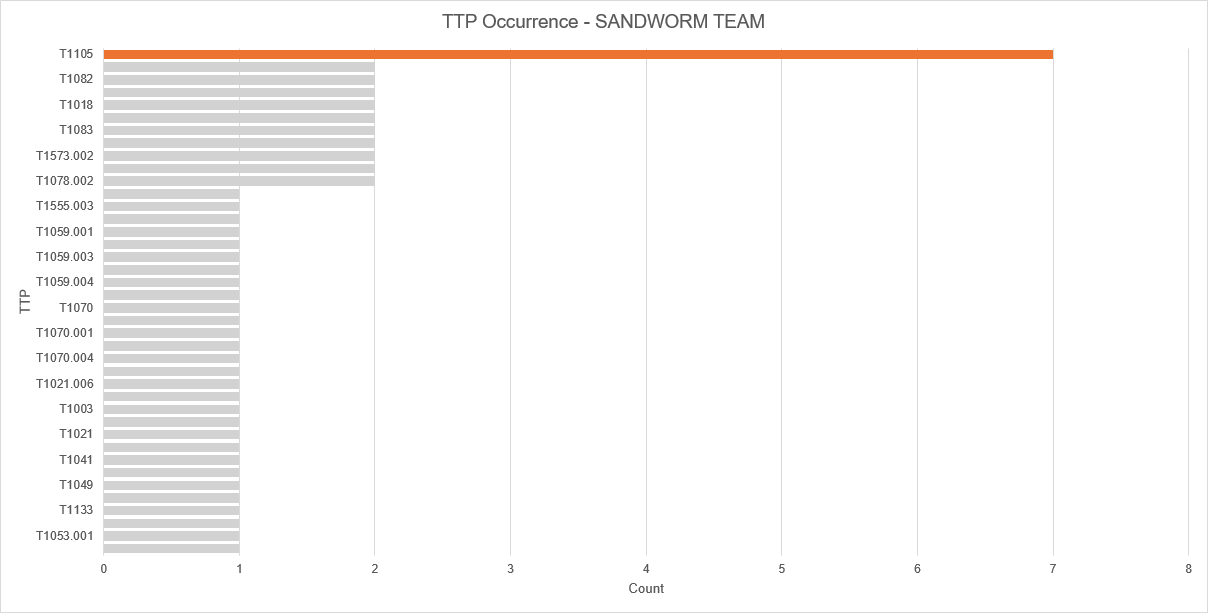
Detection-Ideas-Rules/TTPs/Command and Control/T1105 - Ingress Tool Transfer/Procedures_Windows.yaml at main · vadim-hunter/Detection-Ideas-Rules · GitHub
Aligning Forensic Investigations to the MITRE ATT&CK Framework - Cado Security | Cloud Forensics & Incident Response